
Better Search Replace WordPress Vulnerability Affects Up To +1 Million Sites via @sejournal, @martinibuster
A critical severity vulnerability was discovered and patched in the Better Search Replace plugin for WordPress which has over 1 million active website installs. Successful attacks could lead to arbitrary file deletions, sensitive data retrieval and code execution.
Severity Level Of Vulnerability
The severity of vulnerabilities are scored on a point system with ratings described as ranging from low to critical:
- Low 0.1-3.9
- Medium 4.0-6.9
- High 7.0-8.9
- Critical 9.0-10.0
The severity of the vulnerability discovered in the Better Search Replace plugin is rated as Critical, which is the highest level, with a score of 9.8 on the severity scale of 1-10.
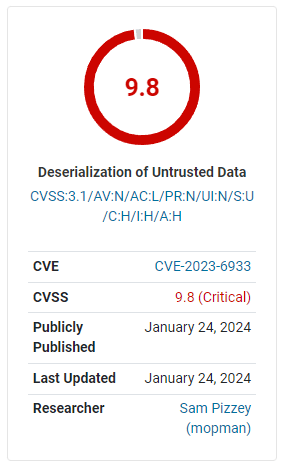 Illustration by Wordfence
Illustration by Wordfence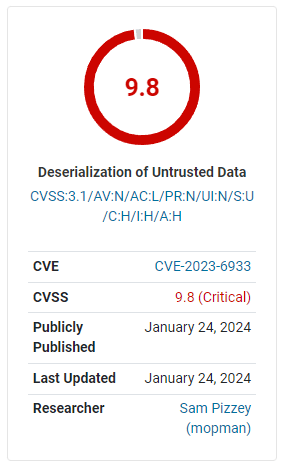
Better Search Replace WordPress Plugin
The plugin is developed by WP Engine but it was originally created by the Delicious Brains development company that was acquired by WP Engine. Better Search Replace is a poplar WordPress tool that simplifies and automates the process of running a search and replace task on a WordPress website database, which is useful in a site or server migration task. The plugin comes in a free and paid Pro version.
The plugin website lists the following features of the free version:
- “Serialization support for all tables
- The ability to select specific tables
- The ability to run a “dry run” to see how many fields will be updated
- No server requirements aside from a running installation of WordPress
- WordPress Multisite support”
The paid Pro version has additional features such as the ability to track what was changed, ability to backup and import the database while the plugin is running, and extended support.
The plugin’s popularity is due to the ease of use, usefulness and a history of being a trustworthy plugin.
PHP Object Injection Vulnerability
A PHP Object Injection vulnerability, in the context of WordPress, occurs when a user-supplied input is unsafely unserialized. Unserialization is a process where string representations of objects are converted back into PHP objects.
The non-profit Open Worldwide Application Security Project (OWASP) offers a general description of the PHP Object Injection vulnerability:
“PHP Object Injection is an application level vulnerability that could allow an attacker to perform different kinds of malicious attacks, such as Code Injection, SQL Injection, Path Traversal and Application Denial of Service, depending on the context.
The vulnerability occurs when user-supplied input is not properly sanitized before being passed to the unserialize() PHP function. Since PHP allows object serialization, attackers could pass ad-hoc serialized strings to a vulnerable unserialize() call, resulting in an arbitrary PHP object(s) injection into the application scope.
In order to successfully exploit a PHP Object Injection vulnerability two conditions must be met:
- The application must have a class which implements a PHP magic method (such as __wakeup or __destruct) that can be used to carry out malicious attacks, or to start a ‘POP chain’.
- All of the classes used during the attack must be declared when the vulnerable unserialize() is being called, otherwise object autoloading must be supported for such classes.”
If an attacker can upload (inject) an input to include a serialized object of their choosing, they can potentially execute arbitrary code or compromise the website’s security. As mentioned above, this type of vulnerability usually arises due to inadequate sanitization of user inputs. Sanitization is a standard process of vetting input data so that only expected types of input are allowed and unsafe inputs are rejected and blocked.
In the case of the Better Search Replace plugin, the vulnerability was exposed in the way it handled deserialization during search and replace operations. A critical security feature missing in this scenario was a POP chain – a series of linked classes and functions that an attacker can use to trigger malicious actions when an object is unserialized.
While the Better Search Replace plugin did not contain such a chain, but the risk remained that if another plugin or theme installed on the same website contained a POP chain that it could then allow an attacker to launch attacks.
Wordfence describes the vulnerability:
“The Better Search Replace plugin for WordPress is vulnerable to PHP Object Injection in all versions up to, and including, 1.4.4 via deserialization of untrusted input.
This makes it possible for unauthenticated attackers to inject a PHP Object.No POP chain is present in the vulnerable plugin. If a POP chain is present via an additional plugin or theme installed on the target system, it could allow the attacker to delete arbitrary files, retrieve sensitive data, or execute code.”
In response to this discovery, WP Engine promptly addressed the issue. The changelog entry for the update to version 1.4.5, released on January 18, 2024, highlights the measures taken:
“Security: Unserializing an object during search and replace operations now passes ‘allowed_classes’ => false to avoid instantiating the object and potentially running malicious code stored in the database.”
This update came after Wordfence’s responsible disclosure of the vulnerability on December 18, 2023, which was followed by WP Engine’s development and testing of the fix.
What To Do In Response
Users of the Better Search Replace plugin are urged to update to the latest version immediately to protect their websites from unwanted activities.





